Decrypt Mac OS Keychain
Elcomsoft Password Digger is a Windows tool for decrypting the content of system and user keychains pulled from a Mac OS computer. The tool exports the full data set into an XML file or builds a filtered dictionary for using with password recovery tools. The system and all user keychains can be decrypted.
Elcomsoft Password Digger enables access to highly sensitive information including Wi-Fi passwords, user’s Apple ID and iTunes passwords, Web site and email account passwords, as well as other sensitive information.
Using Elcomsoft Password Digger together with other ElcomSoft tools opens a way to download iCloud backups created by the user’s iPhone or iPad (via Elcomsoft Phone Breaker), and offers a better chance of breaking other passwords faster by generating a custom dictionary (via Elcomsoft Distributed Password Recovery).
Extract macOS Passwords. Build Custom Dictionary
Elcomsoft Password Digger offers a one-click tool to automatically extract all relevant passwords and save them into a filtered, plain-text dictionary.
Attacking many types of passwords is impossible without a quality dictionary. Even with GPU acceleration, certain types of passwords (such as those protecting Microsoft Office 2010-2013 documents) are just too slow to brute force. A custom dictionary containing the user’s other passwords is invaluable in assisting these types of attacks. By reviewing a list of user’s passwords, experts may be able to derive a common pattern, creating a set of rules for the password recovery tool.
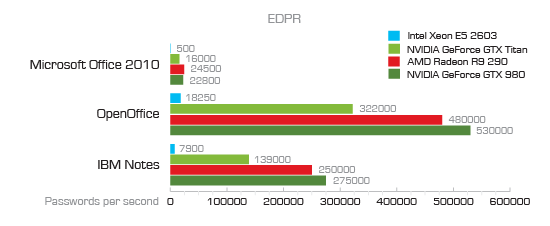
Brute-forcing Microsoft Office 2010 passwords can take ages even with GPU acceleration
Elcomsoft Password Digger can produce highly relevant password dictionaries in one click. By extracting all passwords stored in the user’s keychain and saving them into a plain, filtered text file that only contains the passwords, Elcomsoft Password Digger allows building a highly relevant custom dictionary for breaking strong passwords. The resulting file can be used for dictionary attacks with Elcomsoft Distributed Password Recovery, Elcomsoft Password Recovery Bundle, as well as with individual password recovery tools.
Extract Keychain Data
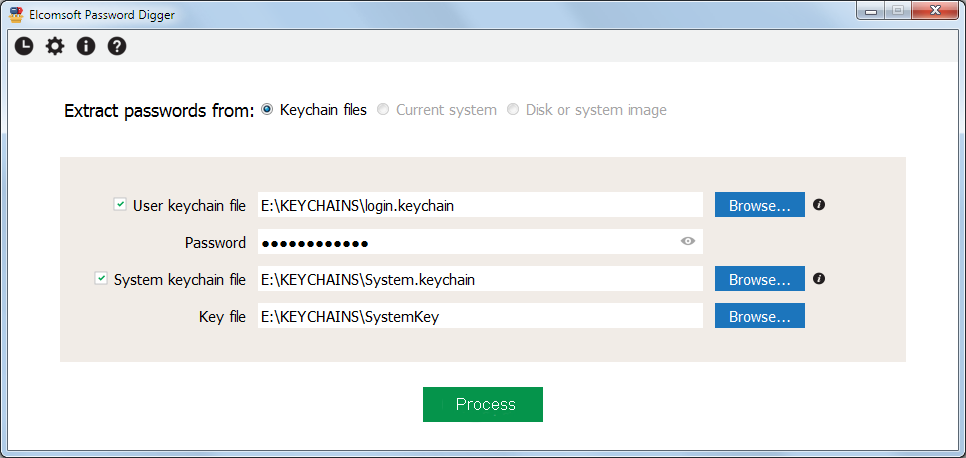
In order to use Elcomsoft Password Digger, experts will need a Windows PC, keychain files extracted from Mac OS, as well as the user’s authentication information (Mac OS login and password or keychain password, if it’s different). For decrypting system keychains, the tool will require a decryption key that must be extracted from the Mac OS computer (administrative privileges are required to extract the file from a live system).
System Keychain
- Keychain file extracted from the user’s Mac OS system
- Decryption key from the same system [1]
User Keychain
- Keychain file extracted from the user’s Mac OS system
- User’s local login password or keychain password (if different)
Features and Benefits
- Gain access to encrypted information stored in Mac OS keychain
- Use extracted Apple ID password to download iCloud backups (with Elcomsoft Phone Breaker)
- Decrypt system and all user keychains obtained from the Mac OS system
- Considerable time savings compared to using Apple Keychain Access
- Export full keychain data into an unencrypted XML file
- Speed up password recovery by producing filtered plain-text files to be used as custom dictionary (with Elcomsoft Distributed Password Recovery and other tools)
-
The decryption key for system keychain must be extracted; administrative privileges are required if extracting from a live system